Context & Data Access Fabric
Controls what enterprise data can be retrieved, why it is relevant, who is authorized to use it, whether it is current, and how it is packaged for execution.
Explore Context Control →
Amalgus provides the governed execution layer for production AI systems: context control, workload orchestration, policy enforcement, evaluation gates, telemetry, evidence capture, and recovery.
The platform integrates with existing enterprise infrastructure so AI workloads can operate across models, agents, tools, data environments, APIs, and human workflows without bypassing authority, security, cost discipline, or operational accountability.
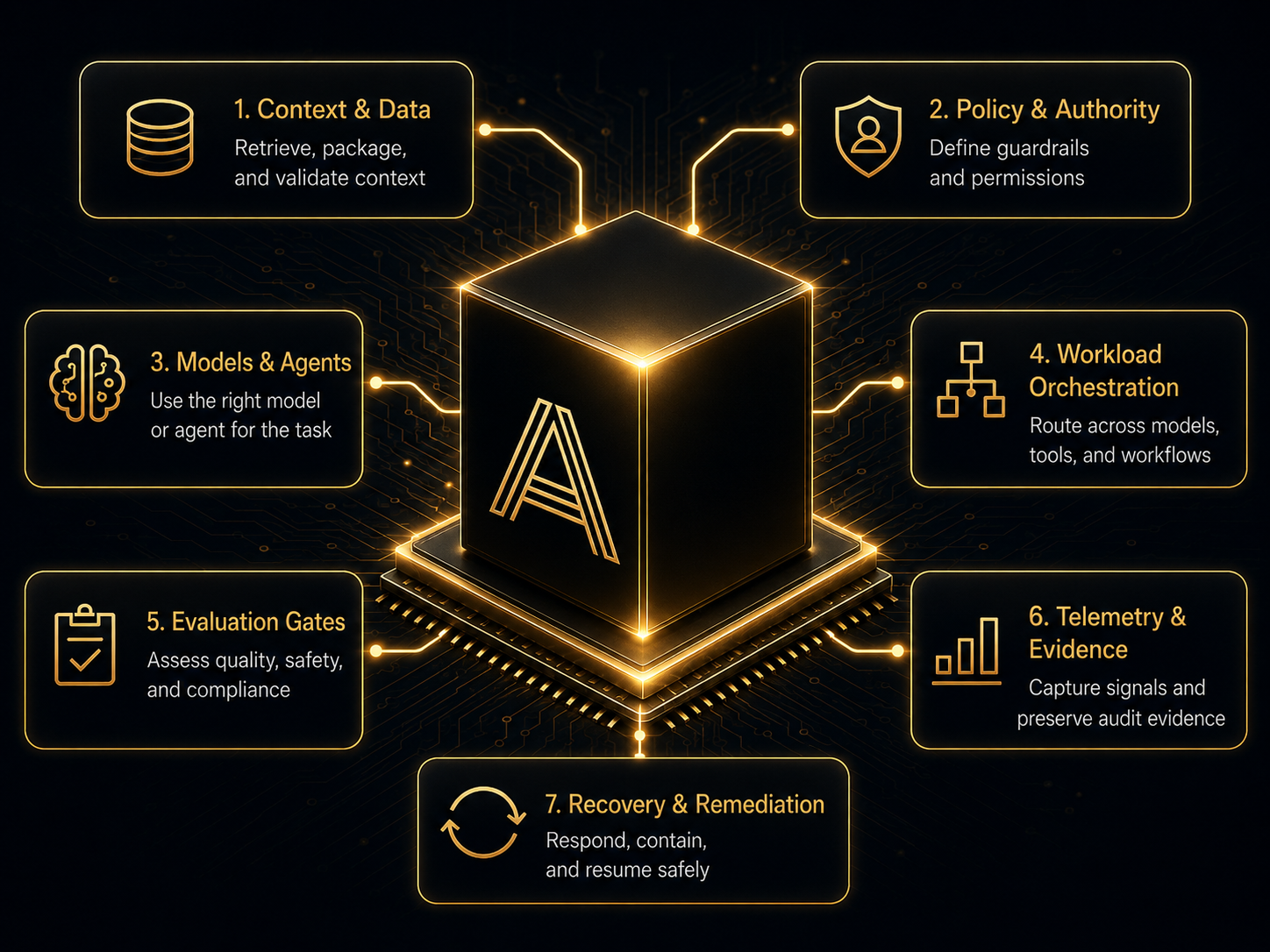
Production AI fails when models, context, tools, policies, evaluations, telemetry, and recovery are managed as disconnected systems. Amalgus coordinates these controls as a single operating layer inside existing enterprise infrastructure.
Controls what enterprise data can be retrieved, why it is relevant, who is authorized to use it, whether it is current, and how it is packaged for execution.
Explore Context Control →
Routes workloads across models, agents, tools, workflows, and compute paths based on task type, risk tier, latency budget, cost target, context size, and required capability.
Explore Workload Orchestration →
Defines what AI systems may access, decide, call, modify, escalate, recommend, release, or block.
Explore Authority Control →
Evaluates whether AI outputs, workflows, tool calls, context packages, and model routes are safe, useful, compliant, and ready to proceed.
Explore Evaluation Gates →
Captures operational telemetry and preserves audit-ready evidence without requiring indefinite storage of every raw prompt, payload, trace, or model output.
Explore Evidence Architecture →
Defines what happens when an AI workload cannot proceed safely.
Explore Recovery Design →

Amalgus does not require a rip-and-replace architecture. The platform integrates with the infrastructure enterprises already operate.
Cloud, hybrid, private cloud, on-prem, air-gapped, edge, containerized, bare-metal, and embedded environments.
Structured systems, operational APIs, document repositories, object and blob storage, event streams, knowledge graphs, cache stores, vector indexes, logs, and runtime signal stores.
Enterprise identity, RBAC, ABAC, policy engines, secrets management, network segmentation, firewall boundaries, approval workflows, and audit controls.
Frontier models, open-weight models, local models, multimodal models, agent frameworks, tool registries, and task-specific execution chains.